



CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: MS Windows
Introduction
CYFIRMA Research and Advisory Team has found Spectra ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Spectra Ransomware
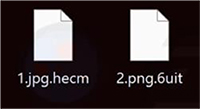
Researchers have recently identified a new ransomware strain named Spectra, which is based on the Chaos ransomware family. Upon execution, Spectra encrypts files and appends a randomly generated four-character extension. It also drops a ransom note titled “SPECTRARANSOMWARE.txt”.
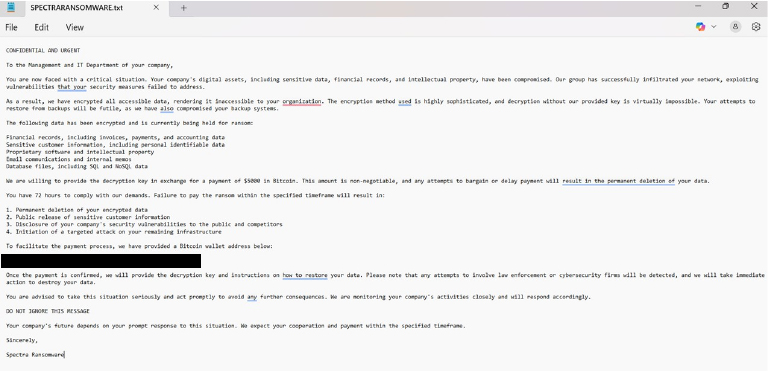
The Spectra ransom note warns victims that their network has been infiltrated, with critical data—including financial records, customer information, proprietary software, and internal communications—encrypted. It further claims that backup systems have been compromised, making recovery impossible without the decryption key.
The attackers demand $5,000 in Bitcoin within 72 hours, threatening to permanently delete the data, leak sensitive information, expose security vulnerabilities, and conduct further attacks if payment is not made. They also caution that involving law enforcement or cybersecurity experts will result in immediate data destruction.

Following are the TTPs based on the MITRE Attack Framework
| Tactic | ID | Technique/SubTechnique |
| Execution | T1053 | Scheduled Task/Job |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1106 | Native API |
| Persistence | T1053 | Scheduled Task/Job |
| Persistence | T1176 | Browser Extensions |
| Persistence | T1542 | Pre-OS Boot |
| Persistence | T1542.003 | Bootkit |
| Persistence | T1543 | Create or Modify System Process |
| Persistence | T1543.003 | Windows Service |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1547.001 | Registry Run Keys / Startup Folder |
| Persistence | T1574 | Hijack Execution Flow |
| Persistence | T1574.002 | DLL Side-Loading |
| Privilege Escalation | T1053 | Scheduled Task/Job |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1543 | Create or Modify System Process |
| Privilege Escalation | T1543.003 | Windows Service |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1547.001 | Registry Run Keys / Startup Folder |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Privilege Escalation | T1574 | Hijack Execution Flow |
| Privilege Escalation | T1574.002 | DLL Side-Loading |
| DefenseEvasion | T1014 | Rootkit |
| DefenseEvasion | T1027 | Obfuscated Files or Information |
| DefenseEvasion | T1036 | Masquerading |
| DefenseEvasion | T1055 | Process Injection |
| DefenseEvasion | T1070 | Indicator Removal |
| DefenseEvasion | T1070.004 | File Deletion |
| DefenseEvasion | T1070.006 | Timestomp |
| DefenseEvasion | T1112 | Modify Registry |
| DefenseEvasion | T1140 | Deobfuscate/Decode Files or Information |
| DefenseEvasion | T1202 | Indirect Command Execution |
| DefenseEvasion | T1222 | File and Directory Permissions Modification |
| DefenseEvasion | T1497 | Virtualization/Sandbox Evasion |
| DefenseEvasion | T1542 | Pre-OS Boot |
| DefenseEvasion | T1542.003 | Bootkit |
| DefenseEvasion | T1548 | Abuse Elevation Control Mechanism |
| DefenseEvasion | T1562 | Impair Defenses |
| DefenseEvasion | T1562.001 | Disable or Modify Tools |
| DefenseEvasion | T1564 | Hide Artifacts |
| DefenseEvasion | T1564.001 | Hidden Files and Directories |
| DefenseEvasion | T1564.003 | Hidden Window |
| DefenseEvasion | T1574 | Hijack Execution Flow |
| DefenseEvasion | T1574.002 | DLL Side-Loading |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1552 | Unsecured Credentials |
| Credential Access | T1552.001 | Credentials In Files |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1087 | Account Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Discovery | T1518 | Software Discovery |
| Discovery | T1518.001 | Security Software Discovery |
| Collection | T1005 | Data from Local System |
| Collection | T1114 | Email Collection |
| Collection | T1115 | Clipboard Data |
| Collection | T1185 | Browser Session Hijacking |
| Command and Control | T1071 | Application Layer Protocol |
| Impact | T1485 | Data Destruction |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
| Impact | T1490 | Inhibit System Recovery |
| Impact | T1496 | Resource Hijacking |
Relevancy and Insights:
ETLM Assessment:
The CYFIRMA assessment indicates that Spectra ransomware poses a significant threat across multiple industries and regions, with a clear focus on targeting enterprises. As ransomware continues to evolve, future variants are likely to incorporate stronger obfuscation and double extortion tactics, increasing risks for organizations—especially those in critical sectors.
Industries such as manufacturing, healthcare, and finance are particularly vulnerable due to their high financial stakes and the sensitive nature of their data, making them prime targets for threat actors.
IOCs:
Kindly refer to the IOCs section to exercise controls on your security systems.
Sigma Rule
title: Delete shadow copy via WMIC
threatname: behaviorgroup: 18
classification: 0 mitreattack:
logsource:
category: process_creation
product: windows detection:
selection: CommandLine:
– ‘*wmic*shadowcopy delete*’ condition: selection
level: critical
(Source: Surface web)
STRATEGIC RECOMMENDATION
MANAGEMENT RECOMMENDATION
TACTICAL RECOMMENDATION
Type: Trojan | Objectives: Financial Theft, Credential Harvesting, Remote Access | Target Industries: Banks, Crypto Financial Services | Target Technologies: Android OS, Cryptocurrency Wallets | Target Geographies: Spain, Turkey
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malware that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week “Crocodilus” is trending.
Crocodilus
Researchers have uncovered Crocodilus, a newly emerging Android banking malware that signals a growing evolution in mobile financial threats. Unlike traditional banking Trojans, Crocodilus arrives fully equipped with remote control capabilities, deceptive overlays, and extensive data theft functions, making it a formidable weapon in the hands of cybercriminals. Initially observed targeting banks in Spain and Turkey, along with cryptocurrency wallets, this malware represents a calculated shift toward high-value financial assets, where the potential for damage is significant. Its ability to blend advanced attack techniques with social engineering tactics puts both banking customers and cryptocurrency investors at risk. As mobile malware continues to evolve, Crocodilus stands out as a highly sophisticated threat with the potential to reshape the mobile banking security landscape.
Attack Method
While the initial access method remains unclear, once it reaches the target device, the malware is installed using a specialized dropper that bypasses Android 13+ restrictions. Following installation, Crocodilus prompts the user to enable Accessibility Services, allowing it to gain deeper control and continue its malicious activities.
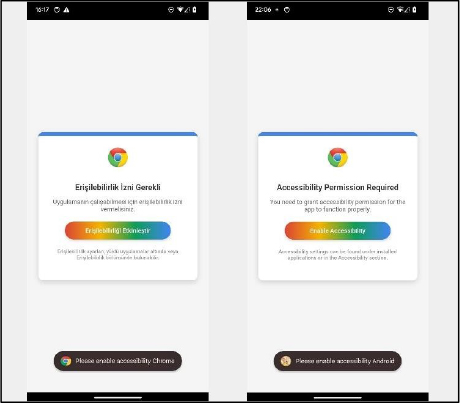
Once the user grants Accessibility Services, Crocodilus connects to its command-and- control (C2) server to receive further instructions, including which applications to target and the overlays to display. The malware operates continuously, monitoring app launches and showing overlays to capture user credentials as they interact with the targeted apps.
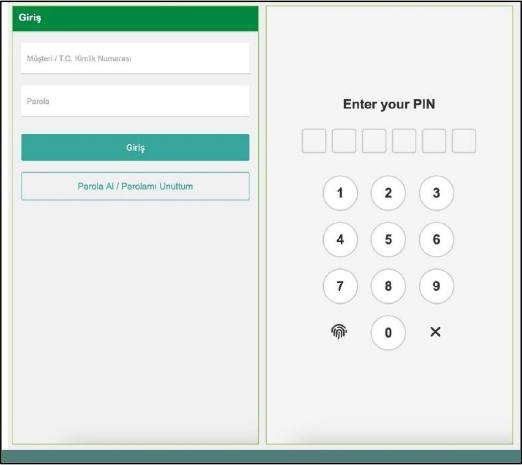
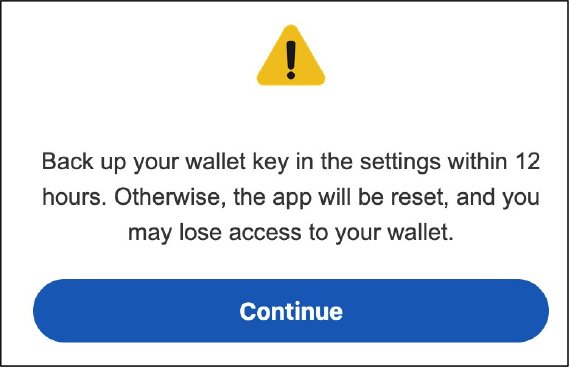
A notable feature of Crocodilus is its use of deceptive overlays to target cryptocurrency wallet users. Once a victim enters their password or PIN, the overlay displays a message warning them to back up their wallet key within 12 hours. It falsely claims that failing to do so will reset the app, potentially locking them out of their funds. This tactic creates a sense of urgency, increasing the chances of victims complying with further malicious instructions. The overlay also guides victims to their seed phrase (wallet key), allowing Crocodilus to capture it using its Accessibility Logger. With access to the wallet’s recovery key, attackers can fully control the wallet and drain its funds.
Another data theft feature of Crocodilus is its keylogging capability, though it functions more like an Accessibility Logger. The malware tracks all accessibility events and captures anything displayed on the screen. This allows it to log all text changes made by the victim, making it similar to a keylogger but with broader capabilities. Additionally, it can execute RAT and bot commands, further enhancing its control over the device.
BOT Commands
| Command | Description |
| TR039OQ1QXZXS | Enablecall forwarding |
| DearTetherDest | Perform USSD request |
| MNKL9G0G9S1XZ | Launchspecified application |
| GoodNightBro | Self-remove from the device |
| TEB9F0S29KWQ | Posta push notification |
| RT90SQ28X1Q | Checkfor available overlays for installed applications |
| KingOnlyDear | Send SMS to specified number |
| KingAllDear | SendSMS to allcontacts |
| KingGetDears | Get contact list |
| KingGetTs | Getinstalled applications list |
| KingBoxSex | GetSMS messages |
| allAdmGet | Request Device Admin privileges |
| TBL03TSMLS | Bulksend of SMSto specified numbers |
| TR9S0XZ | Enableblack overlay |
| ||SettingsNew|| | Updatebot settings |
| ||UpdateTr0x910|| | UpdateC2 settings |
| ||FreeApps|| |
No command, triggers check for created tasksto handle (including overlays download) |
| chzModes | Enable/disable sound |
| mkLoper | Lockscreen |
| CsxStx | Enable/disable remote control session |
| NwSrx | Enable/disable keylogging |
| mrSemploks | Enable/disable self-protection against deletion |
| onlineData | Listof enabled overlay targets |
| innaHotLive | Enable/disable update of the target list |
| SpinderSpike | Makeitself a default SMSmanager |
RAT Commands
| Command | Description |
| InfinityGetTo | Start front camera image streaming |
| InfinityGetStop | Stop front camera image streaming |
| 154856895422 | Wake up device screen |
| TR2XAQSWDEFRGT | Enable/disable “hidden” RAT |
| RightSlider | Right swipe |
| LeftSlider | Left swipe |
| Back_Action | Perform “Back” action |
| Home_Action | Perform “Home” action |
| Menu_Action | Perform “Menu” action |
| 864512532655 | Down swipe |
| 852147414735 | Up swipe |
| 15485666L2 | Lock device |
| M55TRM321XA | Mute phone and enable black overlay |
| PCROC9F9PCROC | Enable sound and remove overlay |
| BL03902910AA | Mute phone and enable black overlay |
| BLD10192OQXX | Enable sound and remove overlay |
| clickScreen | Perform click |
| trXSB123QEBASDF | Perform complex gesture |
| O6155FI2SXZ | Modify text in focused area |
| TCL9CLSKDLX12 | Click a button |
| messagesLenght | Write in focused area |
| TG32XAZADG | Capture screen content for Google Authenticator app |
One of Crocodilus’ RAT commands, “TG32XAZADG,” triggers a screen capture of the content displayed in the Google Authenticator app, using its Accessibility Logging capabilities to extract OTP codes. It records everything displayed on the screen, including OTP names and values, and sends this data to its command-and-control server, allowing attackers to bypass authentication measures in real time. With stolen credentials and personal information, threat actors can fully control a victim’s device using built-in remote access, enabling them to carry out fraudulent transactions undetected. To make this access even more discreet, Crocodilus overlays a black screen to conceal its activities and mutes the device’s sound, ensuring the victim remains unaware of the malicious operations.
INSIGHTS
ETLM ASSESSMENT
From the ETLM perspective, CYFIRMA anticipates that the evolution of Crocodilus signals a future where mobile banking malware increasingly targets high-value financial assets, posing severe risks to individuals. As attackers refine their techniques, fraudulent transactions and credential theft could become more frequent, especially in sectors handling sensitive financial data. With its ability to harvest information undetected, Crocodilus and similar threats may lead to widespread financial losses, forcing stricter security policies and regulatory scrutiny. In the future, its reach may expand beyond Spain and Turkey to a wider range of geographies, particularly regions with growing digital banking adoption and weaker security infrastructure. Advanced social engineering tactics, potentially enhanced by AI, will make deceptive overlays and fake notifications harder to identify, increasing the likelihood of successful breaches. As mobile malware continues to evolve, it’s clear that traditional defenses will no longer suffice, requiring continuous adaptation to mitigate these growing threats.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
STRATEGIC:
MANAGEMENT:
TACTICAL RECOMMENDATIONS
Key Intelligence Signals:
The Return of FamousSparrow: Researchers Unpack New Backdoor Variants and Tactics
Summary:
FamousSparrow is a China-aligned APT group active since at least 2019. It was recently observed targeting government institutions, financial sector organizations, and research entities across North America (United States), Central America (Honduras, Mexico), and other global regions. The group employs sophisticated tactics including exploitation of Microsoft Exchange vulnerabilities particularly ProxyLogon CVE-2021-26855 CVSS Score: 9.8, deployment of ASP.NET webshells, and use of a custom toolset featuring their signature SparrowDoor backdoor – now evolved into modular and parallelized versions. Their July 2024 campaigns revealed new capabilities including integration of the ShadowPad backdoor, advanced process injection techniques (hollowing colorcpl.exe), and refined persistence mechanisms through registry modifications and service creation while maintaining their characteristic use of DLL side-loading and RC4-encrypted payloads with hardcoded keys.
The group’s operations follow a multi-stage compromise chain beginning with initial access through vulnerable internet-facing servers, followed by deployment of webshells (such as s.ashx) that enable PowerShell-based post-exploitation activities including privilege escalation and lateral movement. FamousSparrow has demonstrated continuous toolset development, with their latest SparrowDoor variants showing significant improvements in code quality and introducing parallel command execution capabilities while maintaining overlaps with tools used by related groups like Earth Estries. Their infrastructure employs spoofed TLS certificates mimicking Dell products and utilizes a network of C2 servers (including 216[.]238[.]106[.]150 and 45[.]131[.]179[.]24) that have shown connections to both SparrowDoor and ShadowPad operations.
Recent attacks have revealed FamousSparrow’s expanding targeting scope beyond their original focus on hotels to include financial sector entities in the U.S. and government institutions in Honduras while maintaining their use of both custom malware and shared China-aligned tools alongside publicly available frameworks like PowerHub. The group’s evolving TTPs include memory injection techniques (particularly into wmplayer.exe), LSASS credential dumping using customized tools (dph.dll/msvc.dll), and sophisticated network communication patterns featuring parallelized command channels and proxy functionality. These developments, coupled with their adoption of ShadowPad – a backdoor typically reserved for Chinese threat actors – suggest potential resource sharing within the broader China- aligned threat ecosystem while maintaining distinct operational characteristics.
Relevancy & Insights:
The China-aligned APT group initially gained notoriety for targeting hotels worldwide, along with governments, international organizations, and law firms. Their early campaigns relied heavily on exploiting the ProxyLogon vulnerability (CVE-2021-26855 CVSS Score:9.8) to deploy ASP.NET webshells and their signature SparrowDoor backdoor, which used XOR encryption and simple loader techniques like DLL side-loading (e.g., libhost.dll). During this period, they primarily employed open-source tools like PowerHub for post-exploitation and maintained persistence through registry modifications and service creation, showing a preference for targeting outdated Microsoft Exchange and IIS servers across multiple regions.
The group resurfaced in July 2024 with significantly evolved tactics, targeting a U.S. financial trade group and a Mexican research institute while expanding to governmental entities in Honduras. Their toolset now features two advanced SparrowDoor variants – a parallelized version mimicking Earth Estries’ CrowDoor and a modular plugin-based backdoor – alongside their first documented use of ShadowPad. Notable improvements include RC4 encryption, process hollowing (colorcpl.exe), reflective DLL injection (wmplayer.exe), and sophisticated C2 communications with spoofed TLS certificates. While maintaining their China-aligned profile, these developments demonstrate enhanced stealth capabilities and broader targeting beyond their original hospitality sector focus.
ETLM Assessment:
FamousSparrow has demonstrated consistent targeting of entities across North and Central America, with recent compromises including a U.S.-based financial trade group and a Mexican research institute, alongside historical attacks against government networks in Honduras. The group’s victimology reveals a strategic focus on organizations holding sensitive geopolitical or economic data, with particular interest in sectors like finance, academia, and government institutions. Their operations show a clear evolution from earlier hotel-sector targeting to more traditional intelligence-gathering objectives, suggesting alignment with broader state-sponsored collection requirements. The July 2024 campaigns against financial and research organizations indicate an expansion of targeting priorities while maintaining the group’s signature tradecraft around Microsoft infrastructure exploitation.
Technically, FamousSparrow employs a blended approach combining custom malware families like their signature SparrowDoor backdoor with shared China-aligned tools such as ShadowPad. The group’s toolset has matured significantly, with the latest SparrowDoor variants introducing parallel command execution and modular plugin architectures while maintaining consistent operational patterns like DLL side-loading (K7AVMScn.dll) and process hollowing (colorcpl.exe). Their continued exploitation of ProxyLogon vulnerabilities years after patching, alongside the adoption of newer techniques like TLS certificate spoofing (mimicking Dell certificates) and LSASS memory dumping (via dph.dll/msvc.dll), demonstrates both operational discipline and adaptive tradecraft. The group’s infrastructure overlaps with known ShadowPad networks while maintaining distinct C2 channels (216[.]238[.]106[.]150, 45[.]131[.]179[.]24), suggesting potential resource sharing within the broader China-aligned threat ecosystem.
Strategic Recommendations:
Tactical Recommendations:
Operational Recommendations:
| MITRE FRAMEWORK | ||
| Tactic | ID | Technique |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1133 | External Remote Services |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1106 | Native API |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1218 | System Binary Proxy Execution |
| Credential Access | T1003 | OS Credential Dumping |
| Discovery | T1083 | File and Directory Discovery |
| Collection | T1119 | Automated Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
IOCs:
Kindly refer to the IOCs (Indicators of Compromise) Section to exercise controls on your security systems.
EU to toughen response to hybrid measures
The European Commission is set to enhance EU policing and law enforcement to counter threats from foreign powers like Russia that collaborate with criminal networks, according to a draft of a new internal security strategy. The document outlines plans to expand law enforcement powers to combat “hybrid” attacks by strengthening the EU’s capacity to tackle terrorism, organized crime, and cybercrime, impose sanctions, and access banking information.
“Hybrid threats and open warfare are increasingly indistinguishable,” the document states, highlighting Russia’s “online and offline hybrid campaign against the EU and its allies.”The draft warns that foreign states “exploit crime as a service and use criminals as proxies” to infiltrate critical infrastructure, steal sensitive data, and prepare for future disruptions.
Key proposals include extending the EU sanctions framework—which currently targets terrorists and foreign actors—to include criminal networks and establishing an EU-wide system to track organized crime profits and terrorist financing. This would grant law enforcement broader access to suspect banking transactions.
This initiative to integrate and reinforce the EU’s internal security organizations coincides with Europe’s broader efforts to bolster its defense capabilities, reduce reliance on U.S. support, and address external threats.
ETLM Assessment:
In the 21st century, data flows represent as much a vital lifeline to modern economies as naval shipping does and while privateering disappeared from the oceans, we increasingly see a similar concept being applied to cyber security in recent years. But these information flows on which our digitized economies are ever more dependent are being raided by criminal groups, which have received “license to hack” from their governments. Indeed, the governments of countries like Russia, North Korea, Iran, and China are putting these “digital privateers” to work on their behalf in times of increased tension in international relations. Last couple of months we were able to observe increased institutionalization of digital privateers and their use for de facto undeclared warfare against enemies of the host government.
Chinese hackers conduct cyberespionage across APAC and Latin America
Researchers described cyber espionage activity by the China-linked APT Earth Alux, in which the threat actor is targeting the government, technology, logistics, manufacturing, telecommunications, IT services, and retail sectors across the Asia- Pacific and Latin America. The group typically gains initial access by exploiting vulnerabilities in exposed servers, then deploys its primary backdoor, dubbed “VARGEIT.” Earth Alux then maintains long-term undetected access while exfiltrating “high-value and sensitive information.
ETLM Assessment:
Both Asia and LATAM campaigns seem to be classic examples of state-driven espionage with many similar campaigns like it probably underway at the same time. The campaign is likely part of a broader Chinese strategy to gather intelligence on geopolitical developments and maintain influence around the globe.
Fake headhunting firms target US Federal workers in a Chinese spy game
Media reports have uncovered a covert Chinese tech company using multiple fake consulting and headhunting firms to target recently laid-off U.S. government employees and AI researchers. While its ties to the Chinese government remain unclear, the company’s tactics resemble those used in past Chinese intelligence operations.
Once recruited into the network, former federal employees may be pressured to disclose sensitive government information or suggest additional individuals for potential recruitment—whether knowingly or unwittingly. One fraudulent job listing, for instance, seeks an HR specialist with deep knowledge of Washington’s talent pool to identify candidates with policy or consulting experience and leverage connections within local professional networks, think tanks, and academic institutions.
ETLM Assessment:
Despite the Chinese Embassy to the USA claiming otherwise, the campaign bears all the hallmarks of classic state-driven espionage, including modus operandi often used by Chinese state-hackers. The US and China are in a technological race for domination of the future and will pull no punches or hesitate to use any tricks to get to the top. Thus, we should expect numerous similar campaigns to be ongoing at the same time.
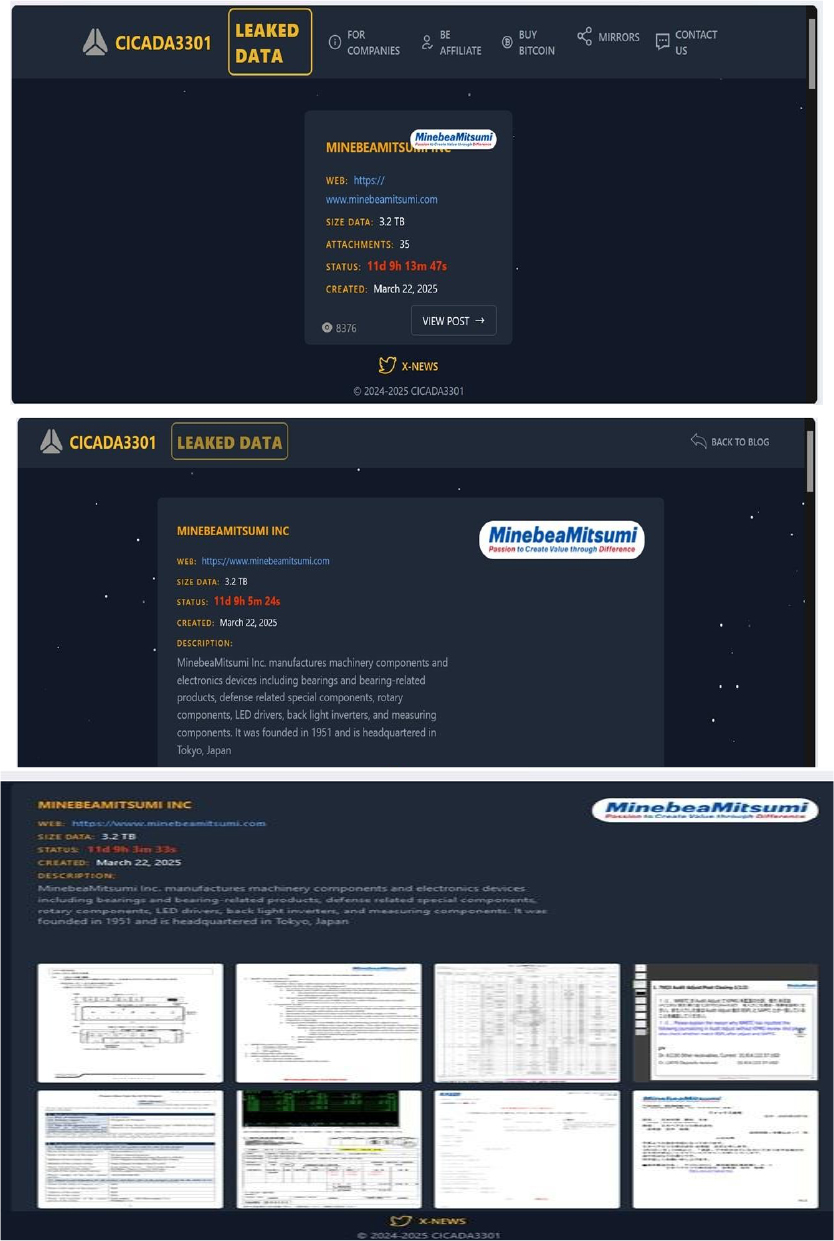
The Cicada 3301 Ransomware Impacts MinebeaMitsumi Inc.
Summary:
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan; MinebeaMitsumi Inc. (https[:]//www[.]minebeamitsumi[.]com/), was compromised by Cicada 3301 Ransomware. MinebeaMitsumi Inc. manufactures machinery components and electronics devices including bearings and bearing-related products, defense-related special components, rotary components, LED drivers, backlight inverters, and measuring components. The compromised data includes confidential and sensitive information belonging to the organization. The total size of the compromised data is approximately 3.2 TB.
Relevancy & Insights:
ETLM Assessment:
Cicada 3301 Ransomware uses sophisticated methods to maintain access to infected systems, allowing attackers to run commands remotely and potentially return for future attacks. The ransomware can target both Windows and Linux systems, including VMware ESXi environments. Based on recent assessments by CYFIRMA, Cicada 3301 Ransomware is expected to intensify its operations across various industries worldwide, with a notable focus on regions in the United States, Europe, and Asia. This prediction is reinforced by the recent attack on MinebeaMitsumi Inc., a leading Manufacturing company in Japan, highlighting Cicada 3301 Ransomware’s significant threat presence in the Asia Pacific.
The RansomHub Ransomware Impacts O-M Ltd
Summary:
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan; O-M Ltd(https[:]//www[.]omltd[.]co[.]jp/) was compromised by RansomHub Ransomware. O-M Ltd is a Japanese manufacturer specializing in machine tools, particularly vertical lathes and other precision machinery. The compromised data includes confidential and sensitive information belonging to the organization. The total size of the compromised data is approximately 300GB.
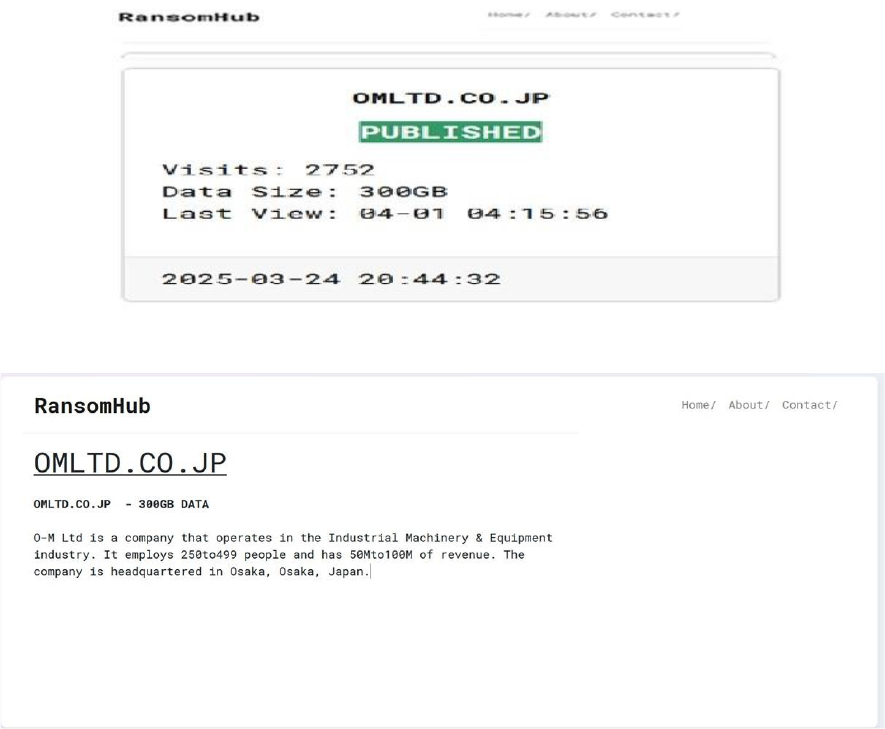
Relevancy & Insights:
ETLM Assessment:
According to recent assessments by CYFIRMA, RansomHub ransomware has rapidly emerged as a significant player in the ransomware landscape since its inception in February 2024. This Ransomware-as-a-Service (RaaS) group has gained notoriety for its sophisticated tactics and cross-platform capabilities, targeting a wide range of sectors including healthcare, finance, and critical infrastructure. RansomHub’s success can be attributed to its ability to adapt and evolve, leveraging advanced evasion techniques and exploiting vulnerabilities in enterprise infrastructure.
Vulnerability in Beego
Relevancy & Insights:
The vulnerability exists due to insufficient sanitization of user- supplied data in the “RenderForm()” function. A remote attacker can trick the victim to follow a specially crafted link and execute arbitrary HTML and script code in user’s browser in the context of a vulnerable website.
Impact:
Successful exploitation of this vulnerability may allow a remote attacker to steal potentially sensitive information, change the appearance of the web page, and perform phishing and drive-by-download attacks.
Affected Products: https[:]//github[.]com/beego/beego/security/advisories/GHSA-2j42- h78h-q4fg
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies, due to a range of vulnerabilities. The following are the top 5 most affected technologies.
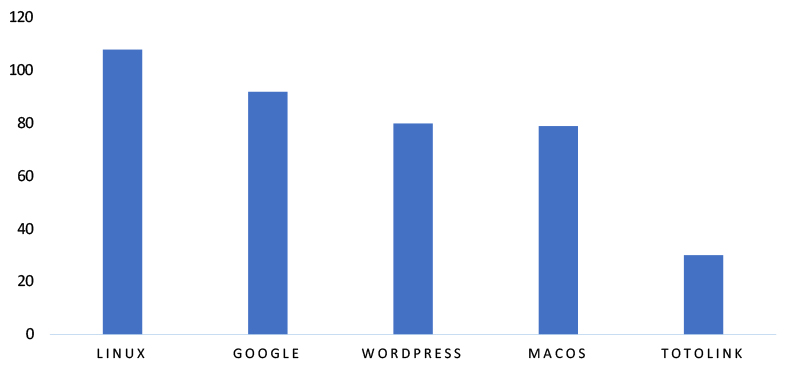
ETLM Assessment
Vulnerability in Beego can pose significant threats to user privacy and security. This can impact various industries globally, including technology, finance, and enterprise application development. Ensuring the security of Beego is crucial for maintaining the integrity and protection of users’ data worldwide. Therefore, addressing these vulnerabilities is essential to safeguarding the rapid development of enterprise applications, including RESTful APIs, web applications, and backend services, across different geographic regions and sectors.
NightSpire Ransomware attacked and published the data of Raja Ferry Port Public Company Limited
Summary:
Recently, we observed that NightSpire Ransomware attacked and published the data of Raja Ferry Port Public Company Limited(https[:]//www[.]rajaferryport[.]com/) on its dark web website. Raja Ferry Port Public Company Limited Thailand is a leading provider of ferry services in the country. Raja Ferry Port offers wharf services and engages in the trade of wharf and passenger ferryboats. The company also provides logistics solutions, including the transportation of fresh produce and fuel products for the private sector. The data leak, following the ransomware attack, encompasses sensitive and confidential records, originating from the organizational database. The total size of the compromised data is approximately 100 GB.
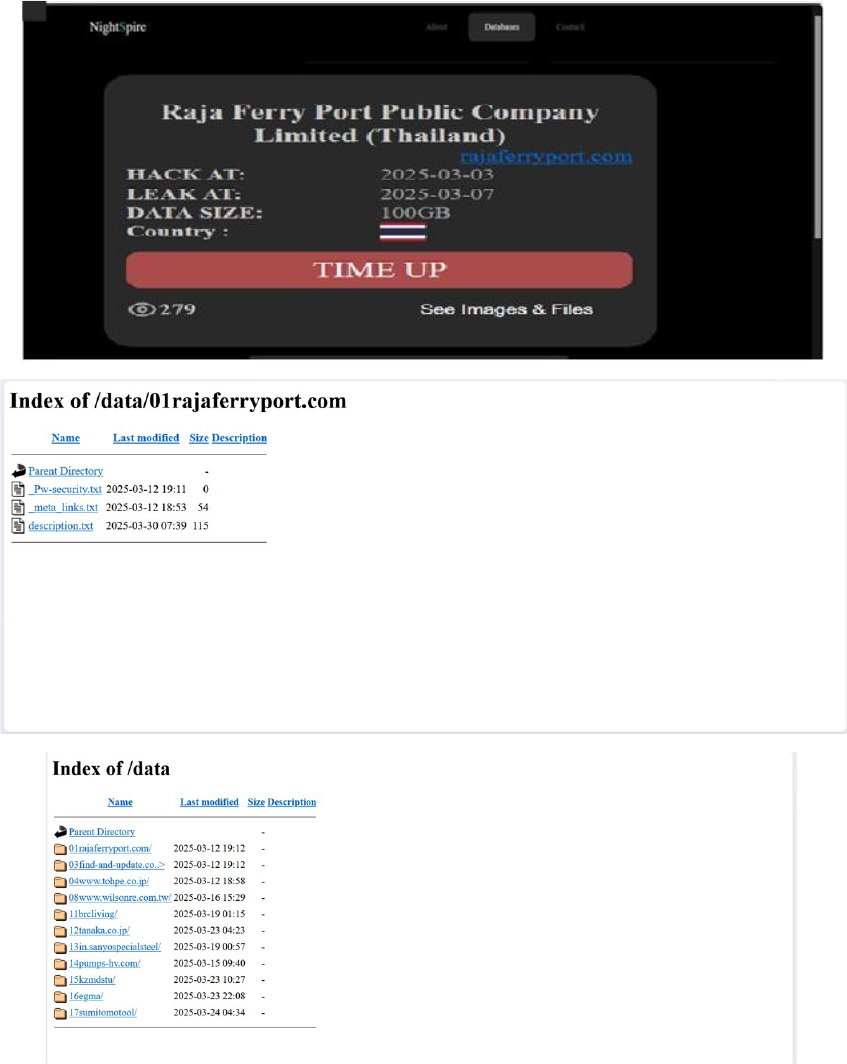
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, NightSpire is a new ransomware group that emerged in early 2025, marking itself as a formidable player in the rapidly evolving ransomware landscape. Despite its recent appearance, NightSpire has already gained attention for its aggressive tactics and well-structured operations.
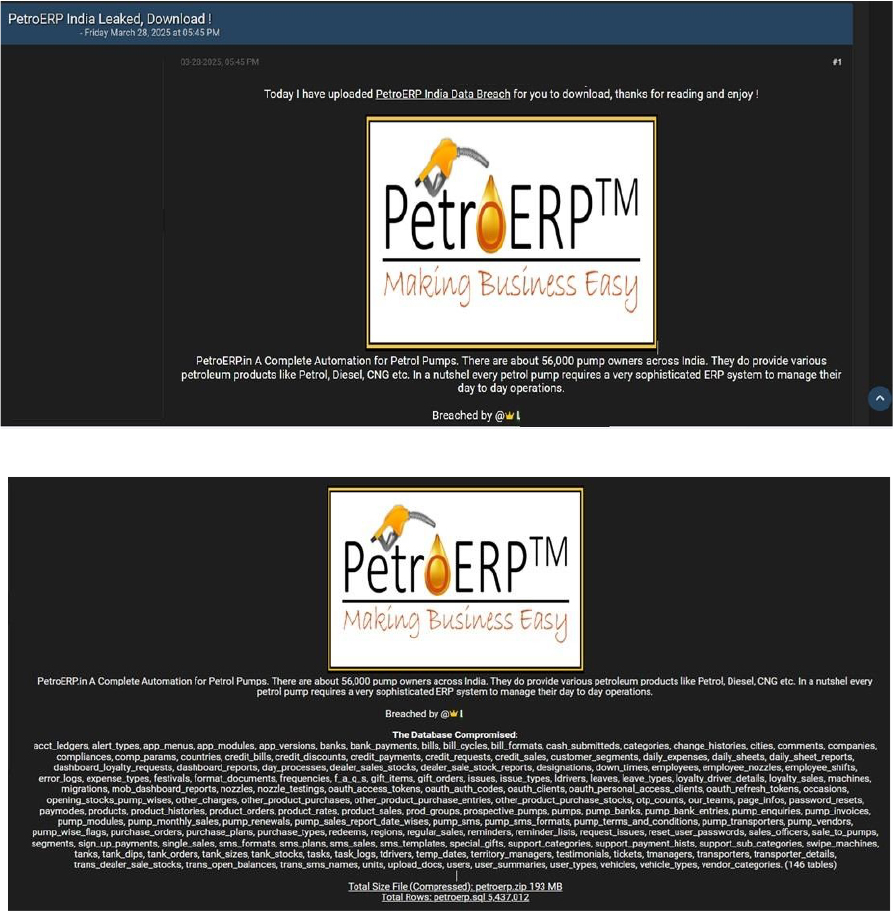
PetroERP India Data Advertised on a Leak Site
Summary:
The CYFIRMA Research team observed a data leak related to PetroERP India (https[:]//petroerp[.]in/) in an underground forum. PetroERP is a comprehensive cloud-based Enterprise Resource Planning (ERP) solution specifically designed for petrol pump management in India. The compromised data includes accounting ledgers, alert types, app menus, app modules, app versions, banks, bank payments, bills, bill cycles, bill formats, and other sensitive and confidential information. The total size of the breached data is approximately 193 MB (compressed). The breach has been linked to a threat actor identified as “LordVoldemort.”
PPSDM KEMENDAGRI REGIONAL BANDUNG Data Advertised on a Leak Site
Summary:
The CYFIRMA Research team observed a data leak related to the PPSDM KEMENDAGRI REGIONAL BANDUNG (https[:]//ppsdmregbandung[.]kemendagri[.]go[.]id/) in an underground forum. Pusat Pengembangan Sumber Daya Manusia (PPSDM) Kementerian Dalam Negeri Regional Bandung is a governmental institution under Indonesia’s Ministry of Home Affairs (Kemendagri) dedicated to enhancing the competencies of civil servants (Aparatur Sipil Negara or ASN) within regional administrations. The compromised data includes admin, member data, book data, visitor records, acquisition records, and loan transactions. The breach has been linked to a threat actor identified as “saTaoz.”
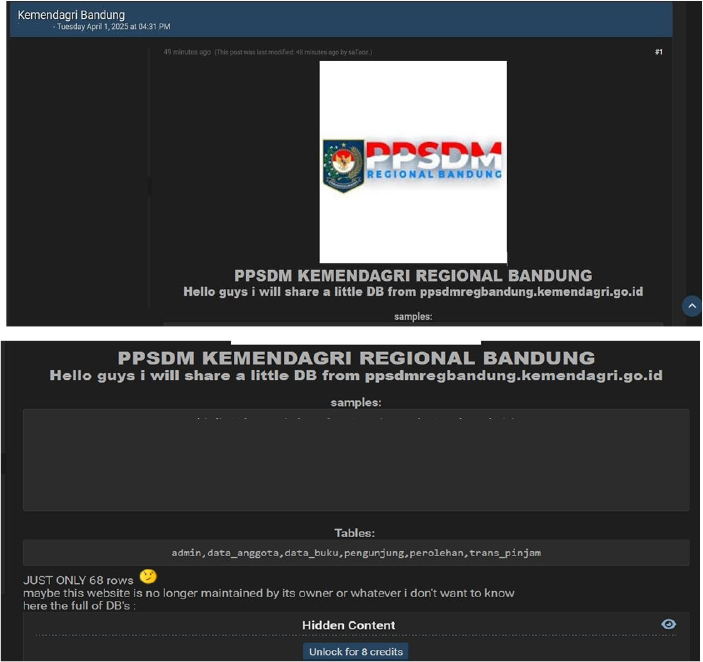
Relevancy & Insights:
Financially motivated cybercriminals are continuously scouring for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to illicitly gain access and steal valuable data. Subsequently, the pilfered data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor claiming the alias “Lord Voldemort” is reportedly involved in acquiring and attempting to sell sensitive data on various underground forums. This activity underscores the persistent risks posed by cyber threat actors who exploit vulnerabilities and engage in data theft. To mitigate these risks, organizations should implement robust security measures, including enhanced monitoring, secure data storage, and regular vulnerability assessments to protect against such malicious activities.
Recommendations: Enhance the cybersecurity posture by:
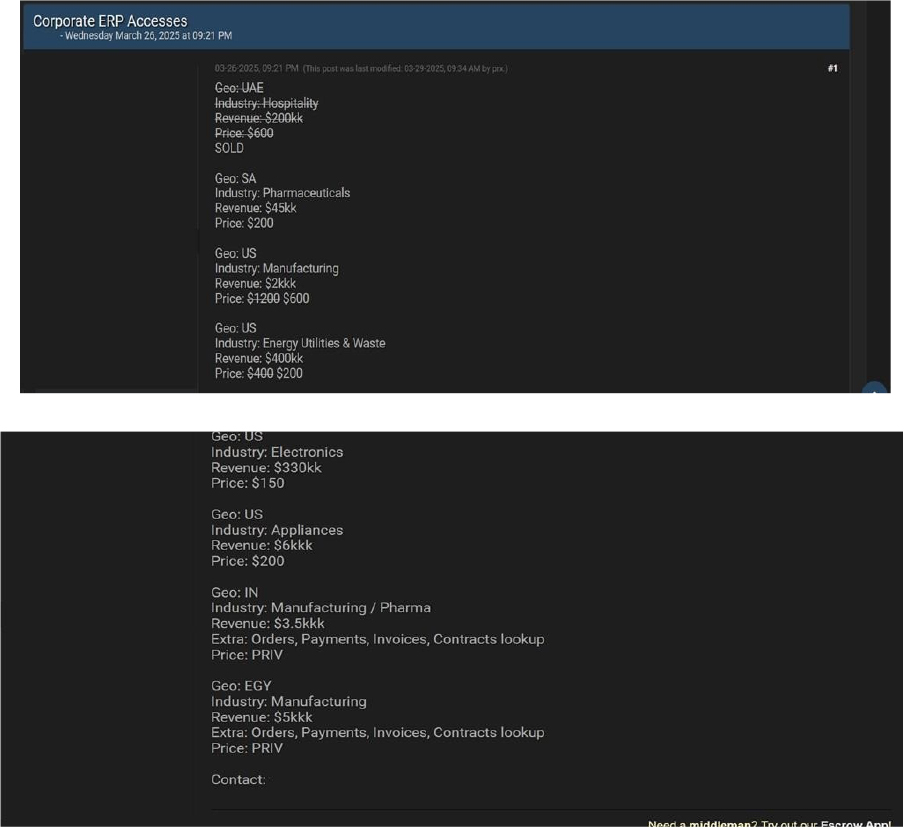
The CYFIRMA Research team observed that a threat actor allegedly offers ERP access to companies in UAE, South Africa, India, Egypt, and the US, spanning several industries including hospitality, pharma, manufacturing & energy.
The CYFIRMA Research team observed that a threat actor has allegedly leaked a database containing GitHub user information on a dark web forum, claiming to have obtained thousands of usernames and emails. While the authenticity of the data remains unverified, the post suggests that the information includes details on high-value GitHub accounts, including OG usernames and top contributors.
According to the forum post, the alleged leak consists of two files: “OG.txt,” which reportedly contains 3,765 lines of usernames and emails belonging to accounts with potentially high resale value, and “Results.txt,” which allegedly includes 826 lines of data on GitHub users with notable contributions and over 1,000 followers
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
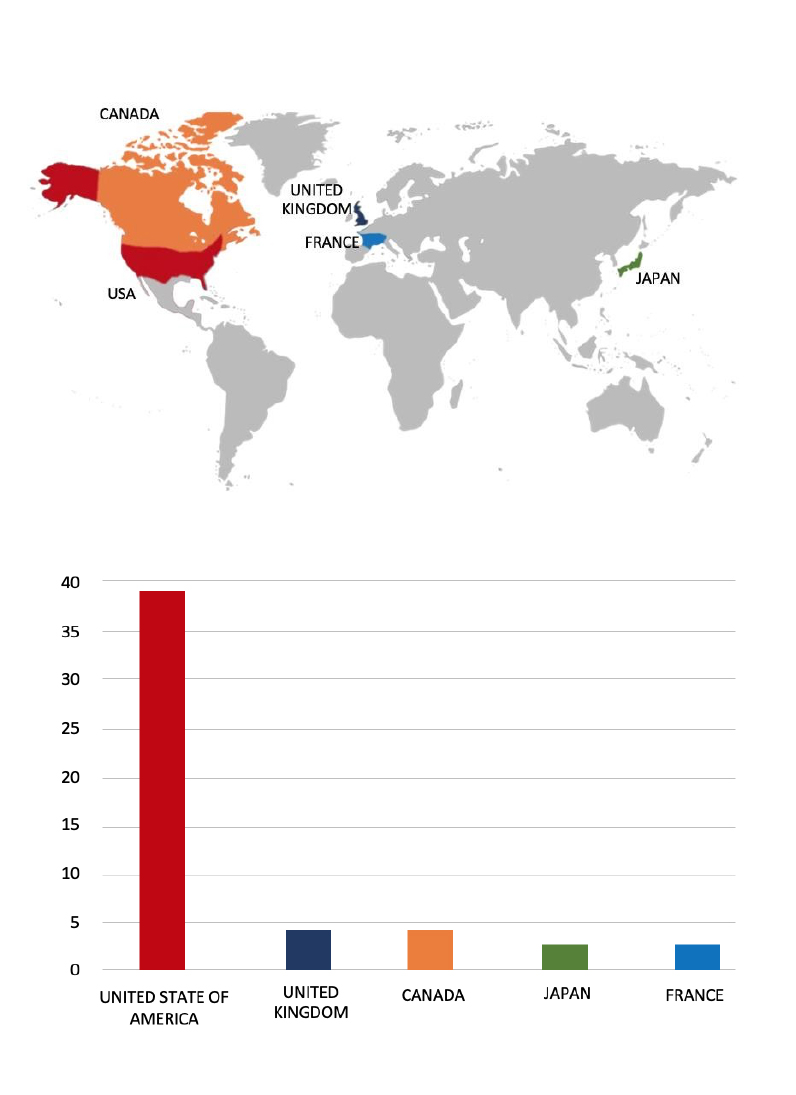
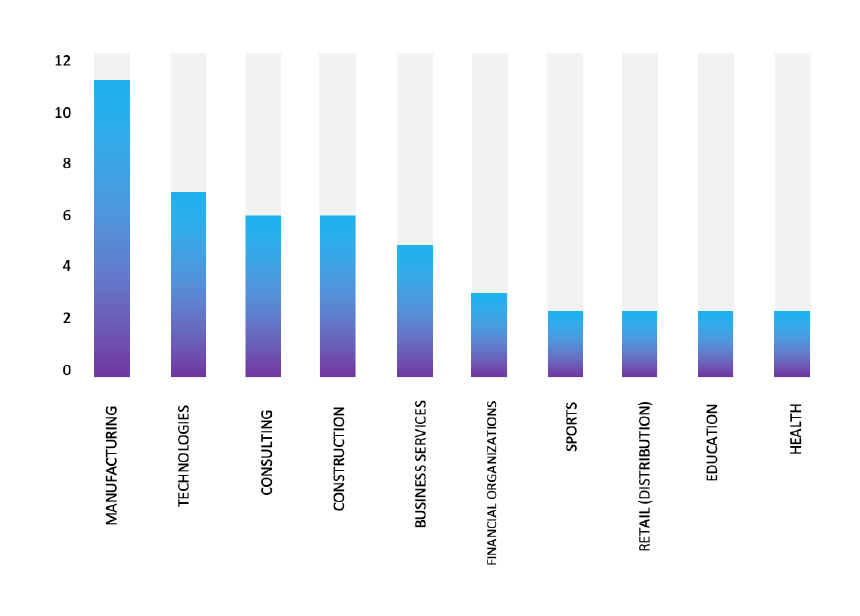
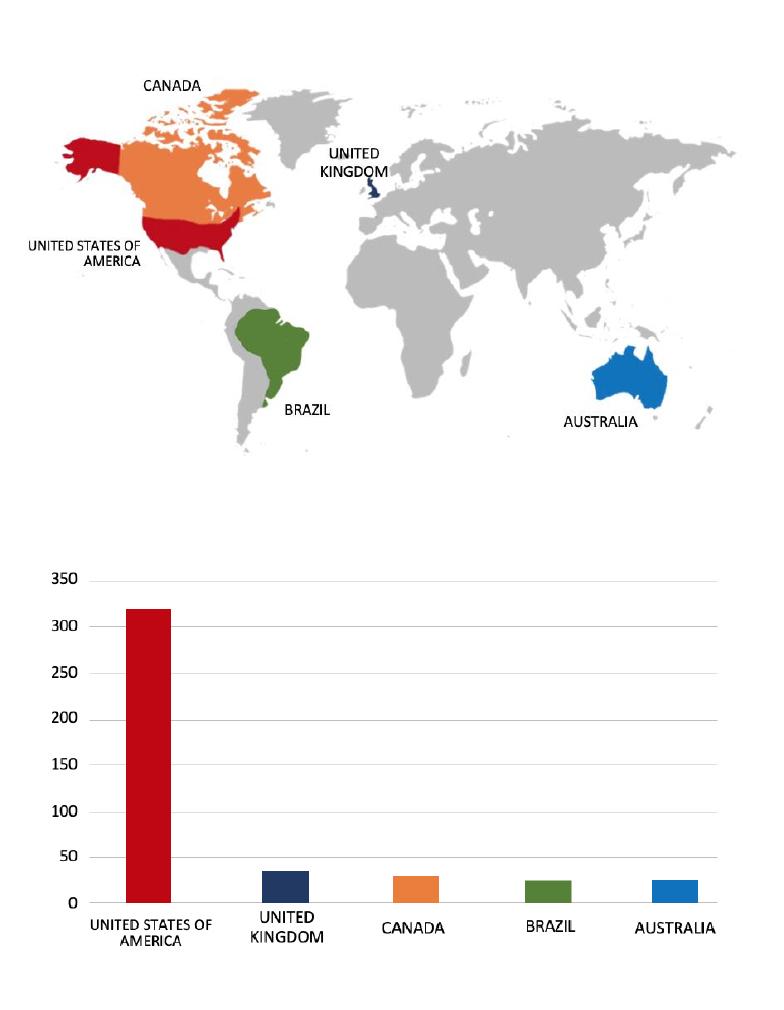
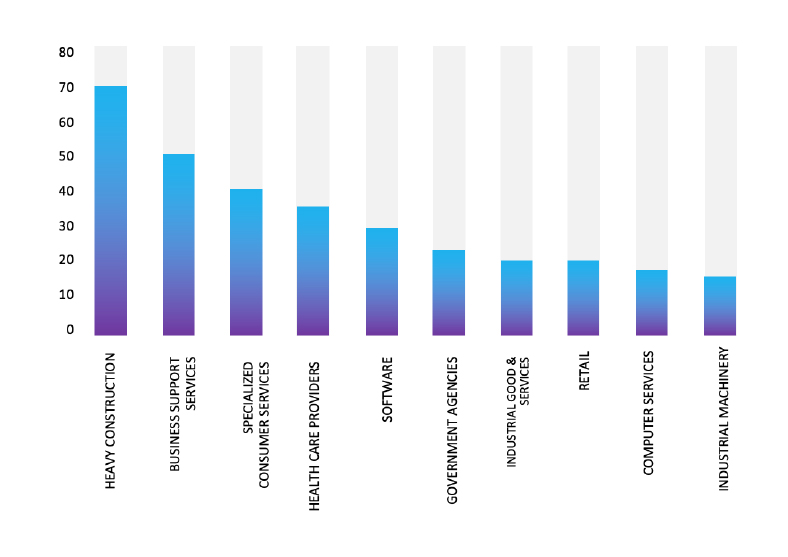
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR