



CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: MS Windows
Introduction
CYFIRMA Research and Advisory Team has found Hush Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Hush Ransomware
Researchers have uncovered a new ransomware strain called Hush, which encrypts victims’ files upon execution and appends a unique victim ID along with the “.hush” extension. Alongside the encryption, the ransomware drops a ransom note in a text file named “README.TXT”, informing victims that their documents, photos, databases, and other critical data have been locked.
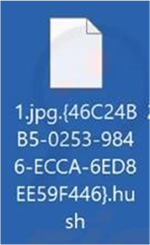
The ransom note states that victims cannot decrypt their files on their own and must purchase a unique private key from the attackers to recover their data. As a form of proof, the attackers offer to decrypt one non-valuable file for free, demonstrating their ability to restore access.
The ransom note provides two email addresses and a Telegram username for victims to contact the attackers. It also includes strict warnings against renaming encrypted files or attempting decryption with third-party tools, as these actions could lead to permanent data loss. To heighten urgency, the note pressures victims to respond within 24 hours, threatening that failure to comply will result in their data being sold or leaked publicly. This tactic aligns with the growing trend of ransomware operators combining encryption with double extortion strategies to maximize their leverage over victims.
Following are the TTPs based on the MITRE Attack Framework
| Tactic | ID | Technique |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1574.002 | Hijack Execution Flow: DLL Side-Loading |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1134 | Access Token Manipulation |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Privilege Escalation | T1574.002 | Hijack Execution Flow: DLL Side-Loading |
| Defense Evasion | T1014 | Rootkit |
| Defense Evasion | T1027.005 | Obfuscated Files or Information:Indicator Removal from Tools |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1134 | Access Token Manipulation |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1574.002 | Hijack Execution Flow: DLL Side-Loading |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Credential Access | T1539 | Steal Web Session Cookie |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1087 | Account Discovery |
| Discovery | T1135 | Network Share Discovery |
| Discovery | T1518.001 | Software Discovery: Security Software Discovery |
| Discovery | T1614.001 | System Location Discovery: System Language Discovery |
| Lateral Movement | T1080 | Taint Shared Content |
| Collection | T1005 | Data from Local System |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1074 | Data Staged |
| Collection | T1114 | Email Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1573 | Encrypted Channel |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
| Impact | T1496 | Resource Hijacking |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA assesses that Hush ransomware poses a significant threat across various industries and geographies. The ransom note from this threat actor clearly indicates targeting enterprises, with techniques like DLL side-loading being employed. As Hush ransomware evolves, future variants are expected to adopt stronger obfuscation and double extortion tactics, heightening the risks for organizations, particularly in critical sectors.
Industries such as manufacturing, healthcare, and finance may be primary targets, given their substantial financial capacity and the sensitive nature of the data they handle.
Sigma Rule
title: Windows Shell/Scripting Application File Write to Suspicious Folder tags:
– attack.execution
– attack.t1059 logsource:
category: file_event
product: windows detection:
selection_1: Image|endswith:
– ‘\bash.exe’
– ‘\cmd.exe’
– ‘\cscript.exe’
– ‘\msbuild.exe’ # https://github.com/elastic/detection- rules/blob/c76a39796972ecde44cb1da6df47f1b6562c9770/rules/windows/defense_ evasion_execution_msbuild_started_by_office_app.toml
– ‘\powershell.exe’
– ‘\pwsh.exe’
– ‘\sh.exe’
– ‘\wscript.exe’ TargetFilename|startswith:
– ‘C:\PerfLogs\’
– ‘C:\Users\Public\’
selection_2:
Image|endswith:
– ‘\certutil.exe’
– ‘\forfiles.exe’
– ‘\mshta.exe’
# – ‘\rundll32.exe’ # Potential FP
– ‘\schtasks.exe’
– ‘\scriptrunner.exe’
– ‘\wmic.exe’ # https://app.any.run/tasks/c903e9c8-0350-440c-8688-
3881b556b8e0/
TargetFilename|contains:
– ‘C:\PerfLogs\’
– ‘C:\Users\Public\’
– ‘C:\Windows\Temp\’ condition: 1 of selection_*
falsepositives:
– Unknown
level: high
(Source: Surface web)
STRATEGIC RECOMMENDATION
MANAGEMENT RECOMMENDATION
TACTICAL RECOMMENDATION
Type: Information Stealer | Objectives: Data theft, Data Exfiltration | Target Technologies: Windows OS, Browsers, Messaging Applications, Cryptocurrency Wallets
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the Week
This week, “SvcStealer” is trending.
SvcStealer
Researchers recently uncovered SvcStealer, a new type of information-stealing malware that spreads through phishing email attachments. First spotted in late January 2025, this malware was written in Microsoft Visual C++ and is designed to collect sensitive data, including system details, installed software, login credentials, and information from cryptocurrency wallets, messaging apps, and browsers. The stolen data is sent to the attacker’s control panel, where they can also deploy additional malware. Cybercriminals behind SvcStealer may sell the stolen data on underground forums and illicit marketplaces, posing a serious risk to victims.
Attack Method
Attackers spread this malware through spear phishing emails that contain malicious Word or Excel attachments. Once opened, the malware silently executes and generates a unique identifier (UID) using the victim’s system information. It then checks if a specific folder already exists in the “C:\ProgramData” directory—if not, it creates one to ensure only a single instance runs on the system. To evade detection, the malware immediately terminates system monitoring tools like Task Manager and other security analysis programs, making it harder for administrators to spot its activity.
After infiltrating a victim’s system, SvcStealer begins gathering sensitive data, starting with cryptocurrency wallet data, which it stores in a dedicated “Wallets” folder. It then extracts details from messaging apps, FTP clients, and browsers, including passwords, credit card information, and browsing history. Additionally, it collects system information, user credentials, installed software details, and a list of running processes. The malware goes further by taking screenshots and stealing targeted file types, such as documents, databases, and encryption keys.
List of Targeted Messengers
List of Targeted Browsers
List of Targeted File Extensions
Once all the stolen data is collected, SvcStealer compresses it into a ZIP file for exfiltration. It then attempts to establish a connection to its command-and-control (C2) server on port 80. After establishing a connection, it uploads the stolen data and registers the victim’s machine in the attacker’s panel. If the connection fails, it continuously retries every five seconds until it is successful. To cover its tracks, the malware deletes the compressed zip file and other stored data, making detection more difficult.
It then generates a unique identifier (UID) based on the victim’s system details and maintains communication with the C2 server, even using backup IP addresses if the primary one is unreachable. Once connected, it captures a screenshot and sends it to the attacker. Additionally, it receives task commands from the C2 server, which may instruct it to download and execute additional malicious files. These files are stored in temporary locations and run on the victim’s system, potentially introducing more threats.
INSIGHTS
ETLM ASSESSMENT
From the ETLM perspective, CYFIRMA anticipates that SvcStealer’s evolution could make it an even more dangerous threat, with future variants possibly adopting advanced evasion techniques to bypass security measures. Its ability to steal a wide range of data might enable more targeted attacks, leading to deeper infiltration and unauthorized access to sensitive information. If its operators expand its functionality, SvcStealer could shift from an information stealer to a more destructive tool, potentially incorporating ransomware or system manipulation features, causing greater financial and operational damage. Additionally, stolen credentials, financial details, and sensitive documents could be traded on underground forums, fueling identity theft, fraud, and further cyber intrusions. As stolen data remains a valuable asset in underground markets, threats like SvcStealer may contribute to a growing ecosystem of digital risks, amplifying security challenges.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
STRATEGIC:
MANAGEMENT:
TACTICAL RECOMMENDATIONS
Key Intelligence Signals:
UAT-5918 targets critical infrastructure in Taiwan
Summary
UAT-5918 is a highly advanced persistent threat (APT) group that primarily targets entities in Taiwan, aiming to establish long-term access for information theft. The group typically gains initial access by exploiting N-day vulnerabilities in unpatched servers exposed to the internet. Following a successful compromise, UAT-5918 conducts extensive reconnaissance to identify key users, domains, and system information. The actor then deploys a combination of open-source tools, including web shells and credential harvesters, to facilitate lateral movement and persistence within victim networks.
The group extensively uses tools like FRP, FScan, In-Swor, Earthworm, and Neo- reGeorg for network reconnaissance, scanning, and maintaining reverse proxy tunnels to compromised systems. Credentials are harvested using utilities such as Mimikatz, LaZagne, and browser credential extractors, enabling further exploitation and lateral movement through techniques like RDP, WMIC, and Impacket. The group also leverages living-off-the-land binaries (LoLBins) to minimize detection.
UAT-5918’s tactics and tools overlap significantly with multiple other APT groups, particularly in their use of common open-source tools and post-compromise behaviors, such as deploying web shells and harvesting credentials. Their operational techniques align with groups involved in cyber espionage campaigns targeting critical infrastructure and telecommunications, particularly in Taiwan. The group is known for creating backdoored user accounts with administrative privileges to ensure ongoing access.
To maintain persistence, UAT-5918 deploys web shells in various subdomains and directories on compromised systems. These web shells are typically used to run reverse shells, allowing the threat actor to execute commands remotely.
Additionally, the group collects and stages data of interest, such as confidential documents and application configurations, for potential exfiltration. Their activities show a clear goal of establishing long-term access to valuable systems while performing continuous reconnaissance and exploiting vulnerabilities within victim networks.
Relevancy & Insights:
UAT-5918, an advanced persistent threat (APT) group, exhibits tactics, techniques, and procedures (TTPs) closely aligning with past campaigns by other Chinese state-sponsored actors, such as Volt Typhoon, Flax Typhoon, Earth Estries, and Dalbit. Similar to these groups, UAT-5918 targets Taiwan, with a focus on critical infrastructure sectors, including telecommunications, healthcare, and IT. Their operations primarily involve exploiting unpatched vulnerabilities in web and application servers to gain initial access, followed by extensive post-compromise activity.
UAT-5918’s use of open-source tools like FRP, In-Swor, and Mimikatz for credential harvesting and lateral movement mirrors previous TTPs observed in Volt Typhoon and Flax Typhoon.
The group relies on web shells, reverse proxies, and tunneling techniques for persistence, and deploys credential extraction tools to harvest valuable data from browsers, registry hives, and other system areas. The consistent pattern of harvesting credentials and creating administrative accounts for sustained access reflects the operational goals of other APT groups like Earth Estries and Dalbit.
These overlaps in tools and tactics suggest UAT-5918 shares similar strategic objectives, namely long-term access for information theft, aligning with past operations observed in Chinese cyberespionage activities.
ETLM Assessment:
UAT-5918 is a sophisticated, China-linked APT group focused on establishing long-term access for information theft and credential harvesting. Their operations center around exploiting unpatched vulnerabilities in internet-exposed web and application servers, enabling them to infiltrate networks. Targeted primarily in Taiwan, UAT-5918 has focused on critical sectors such as telecommunications, healthcare, information technology, and other critical infrastructure.
The group’s tactics involve using a range of open-source tools like FRP, In-Swor, Mimikatz, and various web shells (e.g., Chopper) for post-compromise activities. Their primary objective is information theft, achieved through credential harvesting, port scanning, and lateral movement across compromised networks. UAT-5918 also leverages malware such as FRP and Neo-reGeorg for reverse tunneling and persistence, and credential dumping tools like Mimikatz and LaZagne.
The targeted vulnerabilities mostly involve N-day exploits in web servers, with reconnaissance tactics aimed at identifying weaknesses across exposed endpoints. The threat landscape indicates that UAT-5918’s techniques overlap with other APT groups, including Volt Typhoon, Flax Typhoon, and Earth Estries.
Looking ahead, UAT-5918 is likely to continue using similar TTPs to target high-value organizations in Taiwan and other regions, exploiting known vulnerabilities and leveraging publicly available tools for ongoing access and data theft. Cyber defenders must stay vigilant, patch systems, and deploy advanced detection methods to mitigate this growing threat.
Strategic Recommendations:
Tactical Recommendations:
Operational Recommendations:
| MITRE FRAMEWORK | ||
| Tactic | ID | Technique |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Credential Access | T1056 | Input Capture |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1518.001 | Software Discovery: Security Software Discovery |
| Command and Control | T1071 | Application Layer Protocol |
IOCs:
Kindly refer to the IOCs (Indicators of Compromise) Section to exercise controls on your security systems.
Telegram founder returning to Dubai after a stint in a French jail
The Russian-born founder and owner of the messaging app Telegram, Pavel Durov, announced that he has returned to Dubai after spending several months in France due to a criminal investigation related to activities on the platform.
Durov has confirmed earlier media reports that a French judge had granted him permission to leave the country and go home to Telegram headquarters in Dubai, where it relocated in 2017 and where Durov has also been residing. He became a citizen of the United Arab Emirates in 2021, around the same time he obtained French citizenship.
Durov was arrested at Le Bourget Airport outside Paris in August 2024 and charged with multiple violations related to cyber and financial crimes committed on
Telegram. The platform’s convenience is frequently exploited by hackers and other threat actors to distribute malicious files and disinformation. While authoritarian regimes exploit Telegram to spread propaganda, cybercriminals have also used Telegram as a marketplace for selling hacking tools and as a command-and- control server to exfiltrate stolen user data during cyberattacks.
ETLM Assessment:
Telegram has also been reportedly compromised by the Russian intelligence agencies. While Durov has adopted a largely hands-off approach to moderation on his platform, presenting the app as immune to government influence, French investigation alleges this was not entirely true. Known as the “Mark Zuckerberg of Russia” for co-founding the popular social media platform VKontakte, Durov left Russia in 2014 after reportedly refusing to comply with Moscow’s requests for access to data from Ukrainian users protesting against a pro-Russia government.
Durov has sought to distance himself and the app from Russia, however, many analysts point out the fact his private jet has been repeatedly returning to Russia anytime his business was in trouble and intelligence agencies are thus expecting his platform to be compromised by the Russian state and it is not only possible but also likely that Kremlin may still have ties to or influence over Telegram. This makes the app unsafe for official use and many official agencies thus ban its use.
Top US officials mistakenly leaked war plans on Signal as Russian hackers increasingly focus on the app
In an unprecedented security breach, senior administration officials inadvertently exposed classified military plans when National Security Advisor Mike Waltz accidentally added The Atlantic’s editor-in-chief Jeffrey Goldberg to a private Signal chat group.
The group, which included Secretary of Defense Pete Hegseth and Vice President JD Vance, was discussing detailed plans for an imminent military operation against Houthi forces in Yemen.
The sensitive communications contained specific information about weapons systems, target locations, and operational timing. Goldberg initially doubted the chat’s authenticity until the described military action commenced hours later, confirming the leak’s severity.
While Signal is renowned for its robust encryption, researchers have observed increasing efforts from several Russia state-aligned threat actors to compromise Signal Messenger accounts used by individuals of interest to Russia’s intelligence services.
ETLM Assessment:
Signal has emerged as a prime target for intelligence operations due to its widespread adoption among sensitive user groups. The messaging app’s user base encompasses military and defense personnel, government officials and politicians, journalists and media professionals, human rights activists and dissidents, along with other individuals and groups requiring enhanced security.
The intensified focus on compromising Signal initially stemmed from wartime intelligence requirements during Russia’s invasion of Ukraine, particularly the need to access sensitive government and military communications. However, the tactics and methodologies developed to target Signal are expected to expand beyond this specific conflict.
In the coming months, these sophisticated targeting techniques will likely spread to a broader range of threat actors, including those operating outside the Ukrainian conflict zone. This proliferation suggests a new phase in digital surveillance and intelligence gathering, where successful methods of compromising secure messaging platforms will be adapted and deployed across different geopolitical contexts and regions.
This trend indicates a broader shift in cyber operations, where techniques initially developed for specific military objectives evolve into widely adopted tools in the global intelligence landscape.
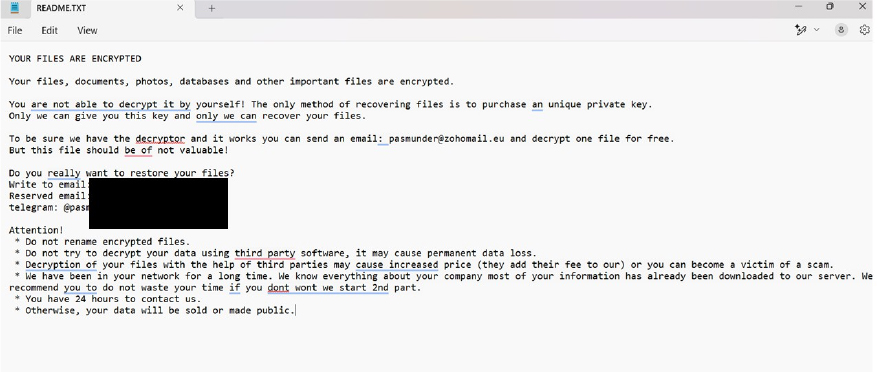
The Qilin Ransomware Impacts SMC Corporation
Summary
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan; SMC Corporation (https[:]//www[.]smcworld[.]com/en-jp/), was compromised by Qilin Ransomware. SMC Corporation is a Japanese company specializing in the development and manufacturing of advanced pneumatic and automation solutions. The compromised data consists of confidential and sensitive information related to the organization. The compromised data totals approximately 1,100 GB and includes 552,000 files.
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Qilin ransomware poses a significant threat to organizations of all sizes. Its evolving tactics, including double extortion (data encryption and leak threats), cross-platform capabilities (Windows and Linux, including VMware ESXi), and focus on speed and evasion make it a particularly dangerous actor.
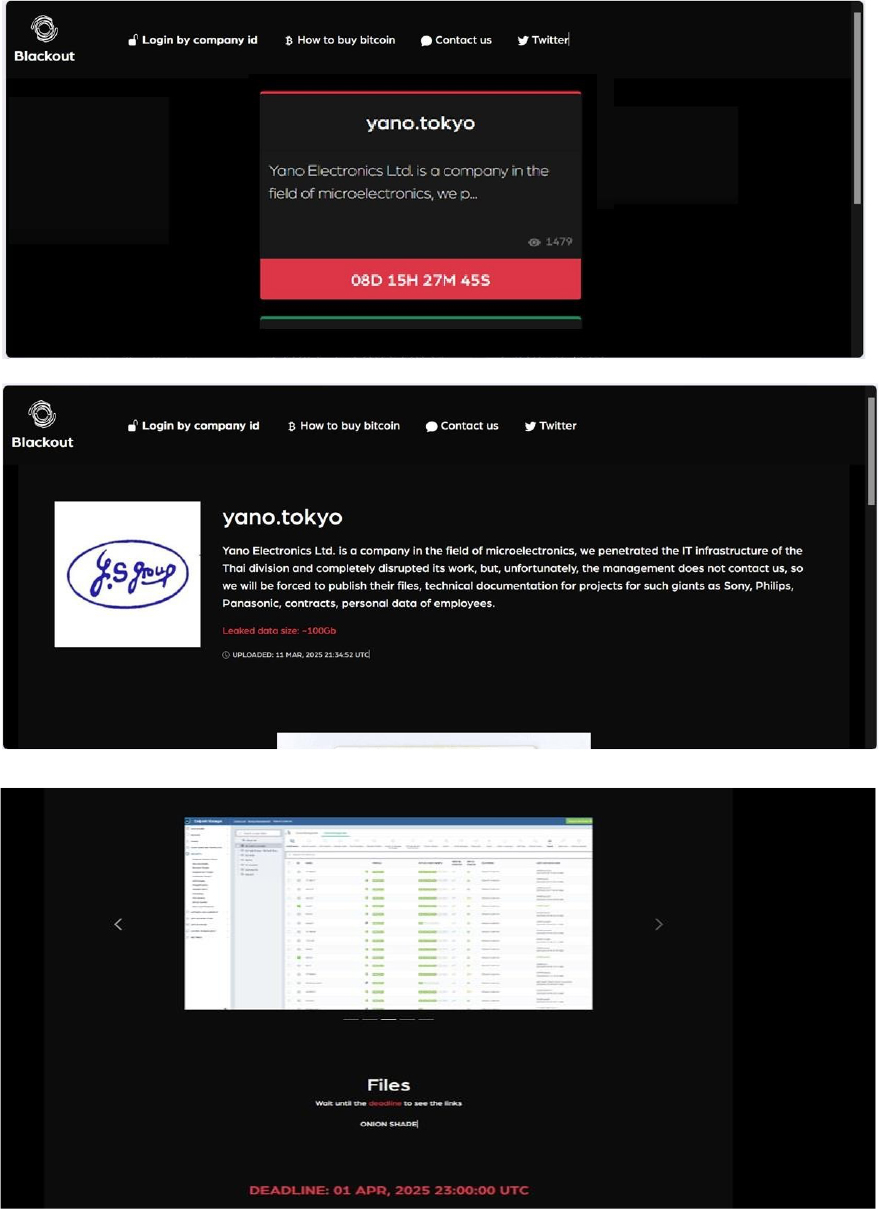
The Blackout Ransomware Impacts Yano Electronics Ltd
Summary:
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan; Yano Electronics Ltd (https[:]//yano[.]tokyo/) was compromised by Blackout Ransomware. Yano Electronics Ltd. is a Japanese company specializing in the manufacturing of precision components and assemblies for various industries. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The ransomware group infiltrated the IT infrastructure of the Thai division, causing a complete disruption of company operations. The compromised data includes technical documentation for projects involving major corporations such as Sony, Philips, and Panasonic, along with contracts and employee personal information. The total volume of compromised data is approximately 100 GB.
Relevancy & Insights:
ETLM Assessment:
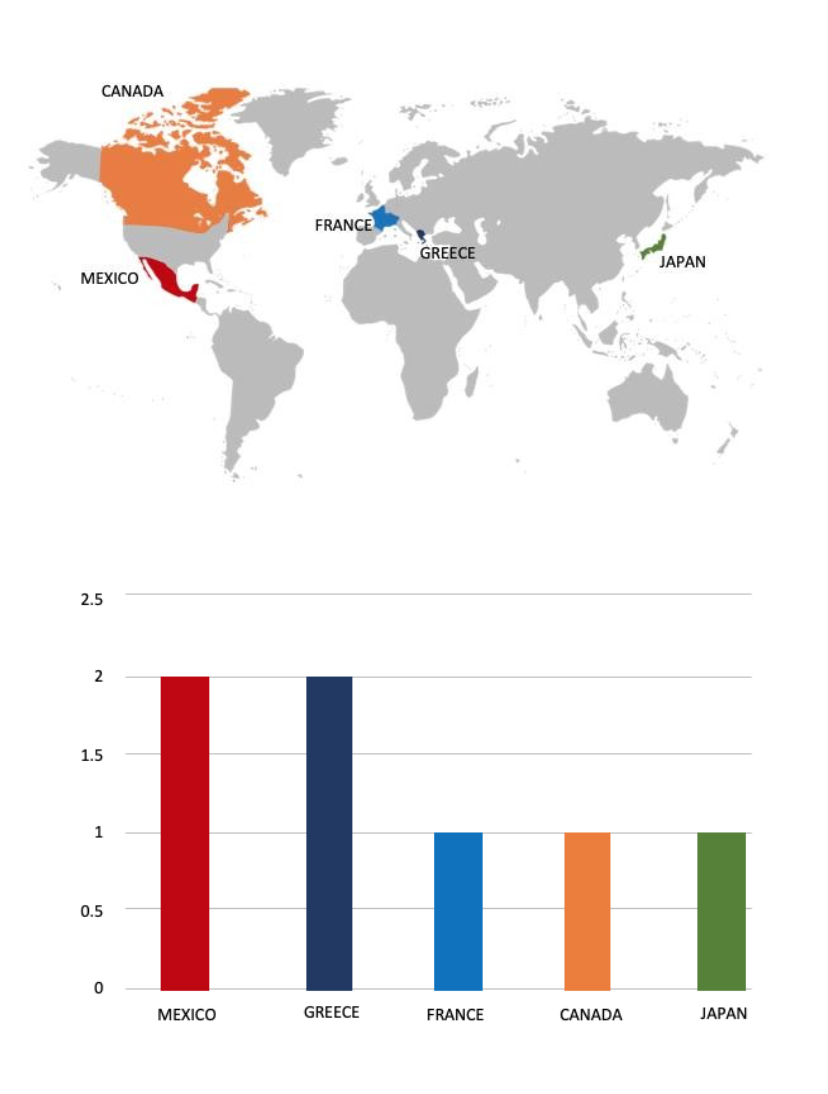
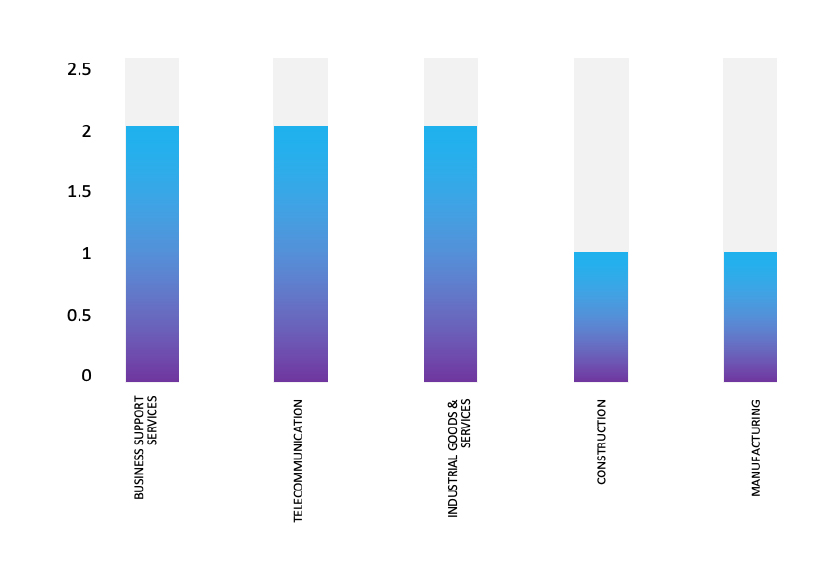
According to recent assessments by CYFIRMA, Blackout Ransomware represents a significant and evolving threat within the current cyber landscape. Its emergence in 2024, coupled with its targeted attacks on diverse sectors across multiple countries, underscores the group’s capacity for widespread disruption. The utilization of standard ransomware tactics, including data encryption, extortion, and the operation of a dark web platform, demonstrates a calculated and potentially sophisticated approach. As a relatively new group, Blackout’s future trajectory and impact remain somewhat uncertain. However, its rapid rise and demonstrated ability to compromise various industries necessitate a heightened state of vigilance and robust cybersecurity measures across all organizations. The ongoing evolution of ransomware threats requires continuous adaptation and proactive defense strategies to mitigate potential damage.
Vulnerability in Gradle
Relevancy & Insights:
The vulnerability exists since the system’s temporary directory can be created with open permissions.
Impact:
A local user can gain elevated privileges on the target system.
Affected Products:
https[:]//github[.]com/gradle/gradle/security/advisories/GHSA- 465q-w4mf-4f4r
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
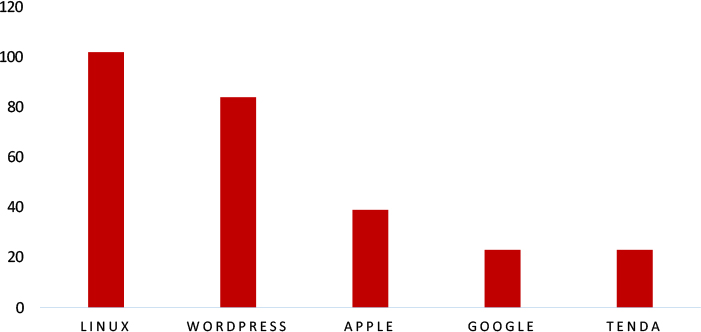
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies, due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in Gradle can pose significant threats to user privacy and security. This can impact various industries globally, including technology, finance, and software development. Ensuring the security of Gradle is crucial for maintaining the integrity and protection of users’ data worldwide. Therefore, addressing these vulnerabilities is essential to safeguarding build automation processes for Java, Android, and Kotlin applications, ensuring secure software development and deployment across different geographic regions and sectors.
DragonForce Ransomware attacked and published the data of Kleen-Pak Products
Summary:
Recently, we observed that DragonForce Ransomware attacked and published the data of Kleen-Pak Products(https[:]//www[.]kleen-pak[.]com/) on its dark web website. Kleen-Pak Products Pte Ltd is a leading manufacturer and supplier in Southeast Asia, specializing in the design, testing, marketing, and distribution of premium-quality hygienic products. Their offerings include wet wipes, pre-moistened beauty mask sheets, sachet products, and wiper sheets, available under both branded and private-label solutions. With a diverse portfolio spanning house brands, private labels, and contract packaging, Kleen-Pak serves a wide range of applications. The company’s operations and manufacturing facility in Singapore are ISO 9001:2008 certified by SGS International and cosmetic GMP certified by the Health Sciences Authority of the Ministry of Health, ensuring the highest production standards. Committed to innovation, Kleen-Pak continuously develops new hygienic products for house brands and private-label customers. Their in-house brands include NUFRESH and BELLO for personal care, MYGENIE and CHAMPS for baby care, KLEEN-UP for home care, and BEST FRIENDS for pet care. The data leak, following the ransomware attack, encompasses sensitive and confidential records, originating from the organizational database. The total size of compromised data is approximately 201.13 GB.

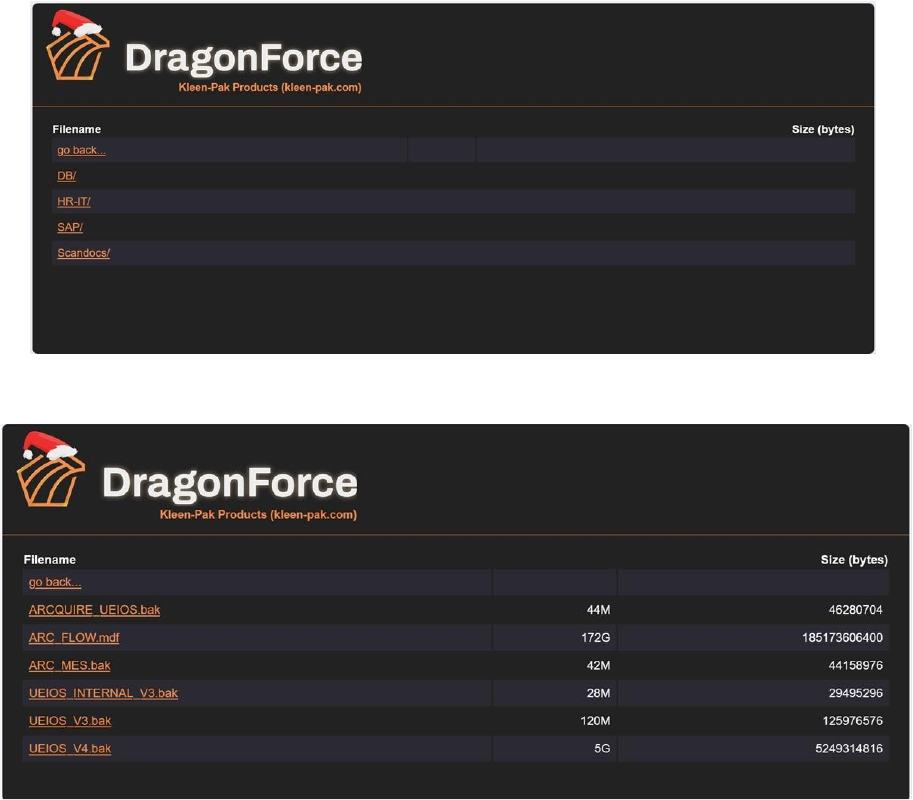
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, DragonForce represents a significant threat in the ransomware landscape due to its advanced operational methods and extensive use of modified ransomware tools. As it continues to target high-profile organizations globally, ongoing vigilance and proactive cybersecurity strategies will be essential for mitigating risks associated with this formidable threat actor.
Organizations should remain alert to the evolving tactics employed by groups like DragonForce to protect their sensitive data and maintain operational integrity.
PT. SKY INDONESIA Data Advertised on a Leak Site
Summary:
The CYFIRMA Research team observed a data leak related to PT. SKY INDONESIA (https[:]//www[.]sky[.]co[.]id/) in an underground forum. PT. Sky Indonesia is a manufacturing company based in Indonesia, specializing in the production of ball- bearing drawer slides and other related products. PT. SKY INDONESIA products are exported to countries such as Japan, China, Hong Kong, Thailand, India, Europe, and the Americas. The compromised data includes ID, contact details, IP address, city, additional information, email, phone number, recipient details (Kepada), name, address, company, country, date (tanggal), profession, and other confidential information. The breach has been linked to a threat actor identified as “saTaoz.”

TADS Co., Ltd Data Advertised on a Leak Site
Summary:
The CYFIRMA Research team observed a data leak related to the TADS Co., Ltd (https[:]//www[.]tads[.]co.th/) in an underground forum. TADS Co., Ltd. is a Thailand- based company specializing in the design, construction, testing, and maintenance of high-voltage electrical systems. They also provide evaluation services for various clients, including industrial plants, power stations, and public and private sector energy projects, for the efficiency of solar panels. The compromised data contains confidential and sensitive information belonging to the organization. The breach has been linked to a threat actor identified as “Alcxtraze.”
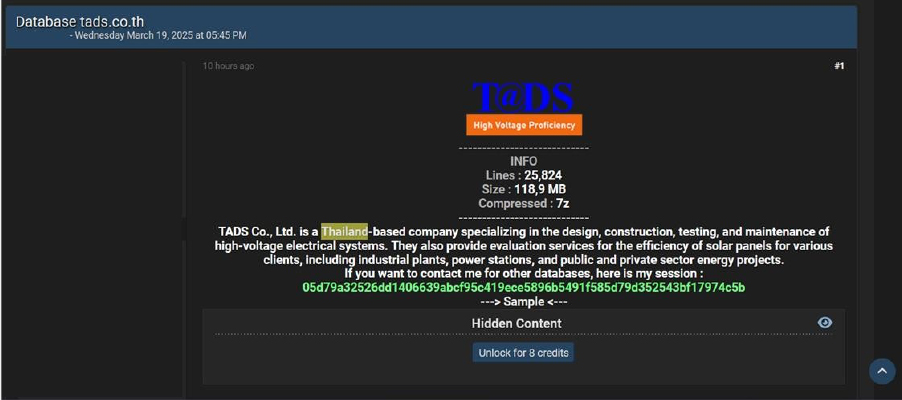
Relevancy & Insights:
Financially motivated cybercriminals are continuously scouring for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to illicitly gain access and steal valuable data. Subsequently, the pilfered data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor “Alcxtraze” has been linked to multiple data breaches, with reports suggesting involvement in accessing and attempting to sell stolen data on dark web forums. The rise of Alcxtraze underscores the persistent danger of cyber-attacks and data breaches driven by dark web activities. As cybersecurity threats continue to evolve, organizations must stay vigilant and implement proactive measures to protect sensitive information.
Recommendations: Enhance the cybersecurity posture by:
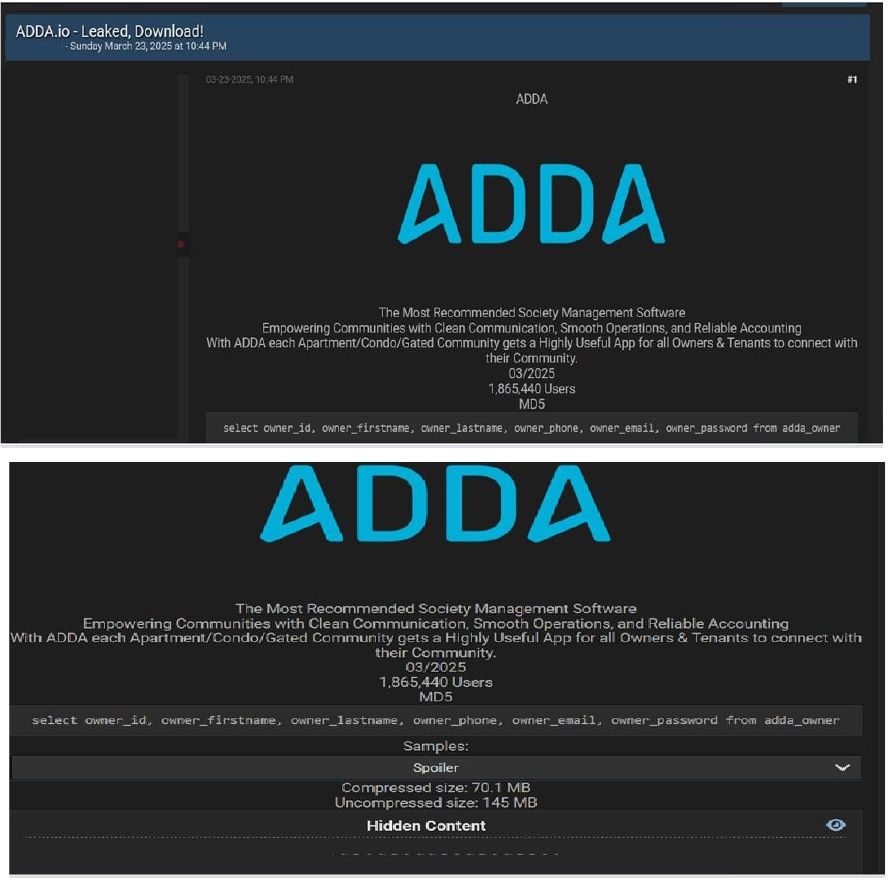
The CYFIRMA Research team observed a data leak related to the ADDA in an underground forum. ADDA[.]io is a comprehensive Software as a Service (SaaS) platform designed for residential community management. ADDA offers a suite of tools aimed at streamlining the administration of apartment complexes, condominiums, gated communities, and homeowners’ associations (HOAs). The breached data includes the owner’s ID, first name, last name, phone number, email address, password, and other confidential information from ADDA owners. The total size of the compromised data is approximately 145 MB.
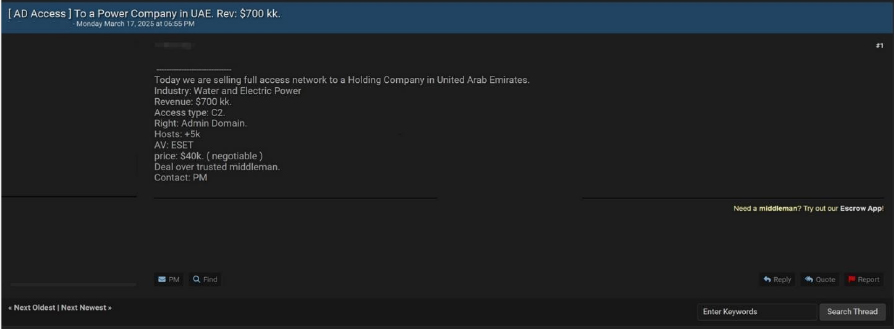
The CYFIRMA Research team observed a threat actor allegedly claimed to be selling network access to a major power company in the United Arab Emirates. The threat actor claims to have administrative domain access to a holding company operating in the water and electric power sector. The perpetrator purportedly is offering this access for $40,000, though indicating the price is negotiable.
The post details that the compromised network reportedly contains over 5,000 hosts protected by ESET antivirus software. The company supposedly generates approximately $700 million in revenue, making it a potentially significant target.
The threat actor claimed the access was available through a command and control (C2) server and suggested conducting the transaction through a trusted intermediary.
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
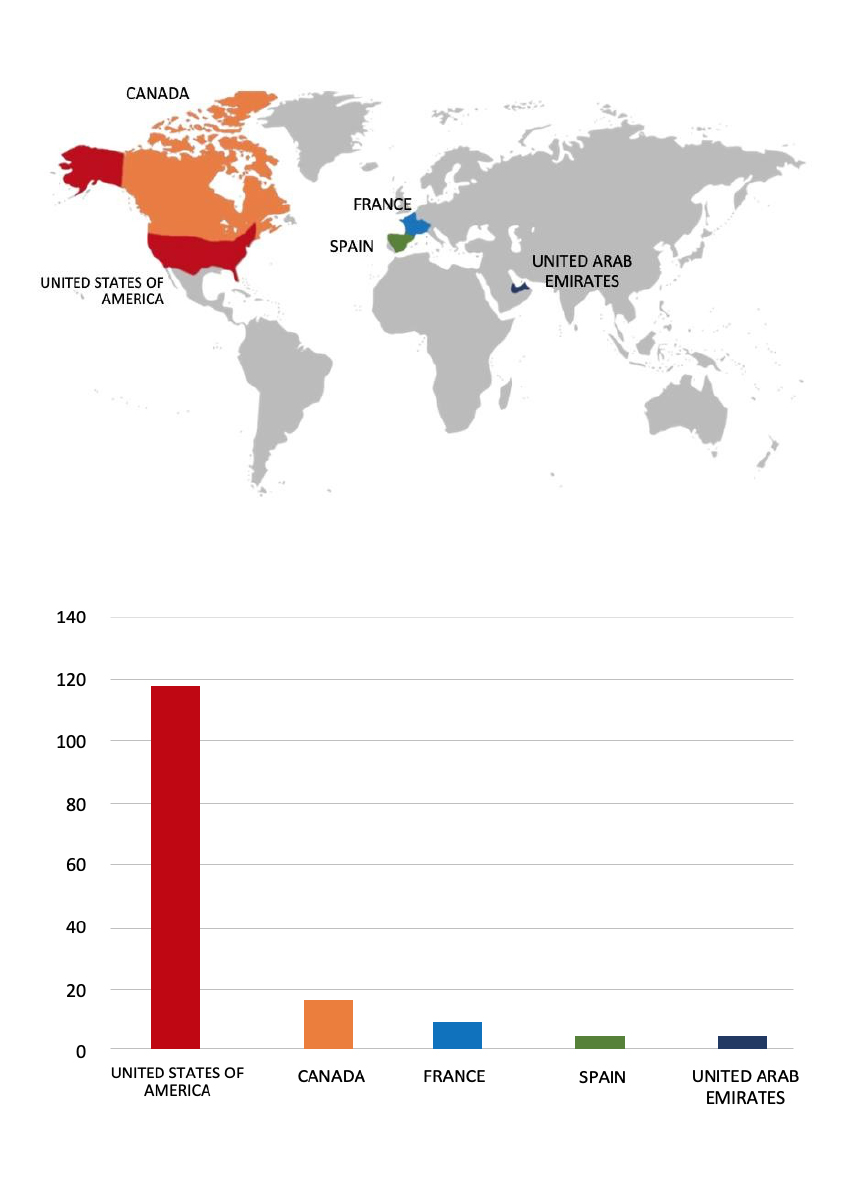
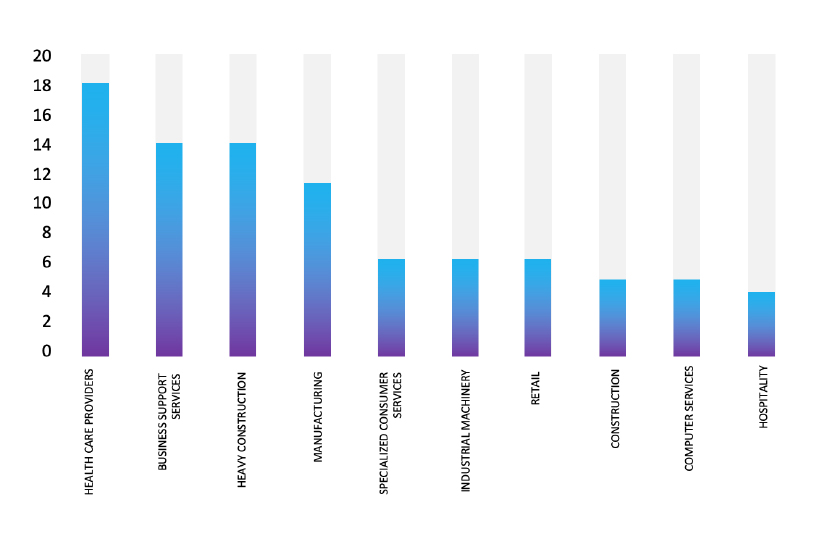
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.